$250K: That’s what Lenovo earned to RAT YOU OUT with Superfish • The Register
$250K: That's what Lenovo earned to RAT YOU OUT with Superfish • The Register.
$250K: That's what Lenovo earned to RAT YOU OUT with Superfish • The Register.
NSA inquiry chief suffers phone tampering – The Local.
“FREAK” flaw undermines security for Apple and Google users, researchers discover.
Facebook posts from U.S. land Pinellas contractor in Arab jail | TBO.com and The Tampa Tribune.

Rogue Router Firmware Chaos #Backdoor | Entrust:Blog.
FCC overturns state laws that protect ISPs from local competition | Ars Technica.

FCC approves net neutrality rules, reclassifies broadband as a utility.

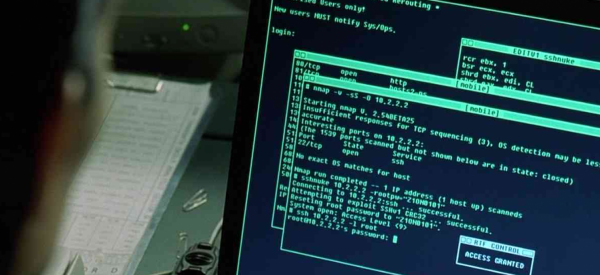
Hacker Claims Feds Hit Him With 44 Felonies When He Refused to Be an FBI Spy | WIRED.
Russian researchers expose breakthrough U.S. spying program | Reuters.