HTTPS can’t be trusted to obscure private online activity
HTTPS can't be trusted to obscure private online activity.
HTTPS can't be trusted to obscure private online activity.
Red Hat programmer discovers major security flaw in Linux.
BBC News – New magnetic material could boost electronics.

Critical crypto bug leaves Linux, hundreds of apps open to eavesdropping | Ars Technica.
Apple's iCloud security feature in OSX is bypassed in just 70 lines of code – Neowin.

GCHQ identified Kinect as possible snooping tool; Microsoft denies all knowledge | Games industry news | MCV.
How Steve Perlman's "Revolutionary" Wireless Technology Works – and Why its a Bigger Deal than Anyone Realizes.
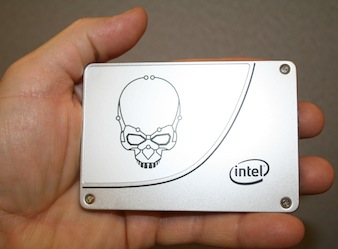
Intel kills SSD overclocking, unleashes its fastest-ever consumer drive – Computerworld.
Infographic: New Ponemon SSH Security Vulnerability Report – Venafi.

RSA security attack demo deep-fries Apple Mac components – Network World.